Monitoring and Detecting DDoS Attacks: Tools and Techniques
DDoS attacks have become a major concern for businesses and organizations worldwide. With the increasing frequency and sophistication of these attacks, it is crucial to have effective tools and techniques in place for monitoring and detecting them. One such tool is network traffic analysis, which involves inspecting and analyzing network traffic patterns to identify any abnormal behavior. By monitoring the volume, frequency, and types of traffic, anomalies can be detected and potential DDoS attacks can be identified in real-time.
Another important technique is the use of intrusion detection and prevention systems (IDPS). These systems work by continuously monitoring network traffic and comparing it against a database of known attack signatures. If a matching signature is found, the IDPS can take immediate action to block or mitigate the attack. Additionally, behavioral analysis can be employed to identify deviations from normal user behavior, allowing for the detection of DDoS attacks that may not have a specific signature. By combining these tools and techniques, organizations can strengthen their defenses against DDoS attacks and minimize the impact of potential disruptions to their network infrastructure.
Case Studies: Real-life Examples of Successful DDoS Attack Mitigation
DDoS attacks are a widespread threat that target various industries, including financial institutions, e-commerce platforms, and online gaming companies. These malicious attacks can cause significant financial losses and damage a company’s reputation. However, through effective mitigation strategies, organizations have managed to successfully defend against DDoS attacks and safeguard their systems and networks.
One notable case study involves a leading e-commerce platform that experienced a massive DDoS attack, resulting in severe downtime and loss of revenue. To counter this attack, the company implemented a robust DDoS mitigation solution, which involved a combination of traffic analysis, rate limiting, and IP blocking. By proactively identifying and filtering out malicious traffic, the company reduced the impact of the attack and ensured uninterrupted service for its customers. This successful mitigation strategy not only protected the company’s reputation but also instilled confidence among its customers, reinforcing the importance of investing in robust DDoS defense mechanisms.
• The leading e-commerce platform implemented a robust DDoS mitigation solution
• The solution involved traffic analysis, rate limiting, and IP blocking
• Proactive identification and filtering of malicious traffic reduced the impact of the attack
• Uninterrupted service for customers was ensured through successful mitigation
• The company’s reputation was protected and customer confidence was reinforced
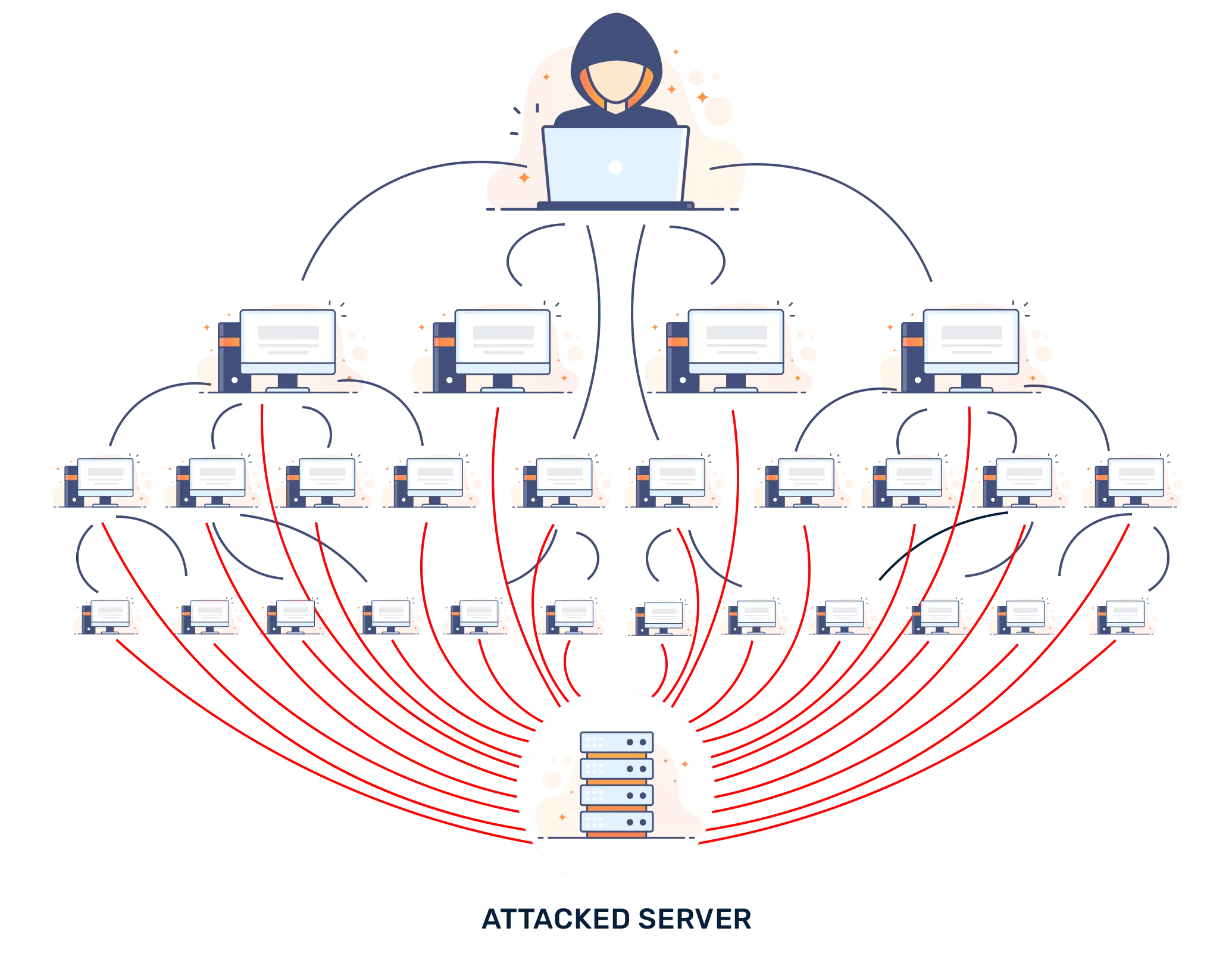
What is a DDoS attack?
A Distributed Denial of Service (DDoS) attack is a malicious attempt to disrupt the regular functioning of a network, service, or website by overwhelming it with a flood of internet traffic from multiple sources.
How can you monitor and detect DDoS attacks?
Various tools and techniques can be used to monitor and detect DDoS attacks, including network traffic analysis, anomaly detection systems, and specialized DDoS detection and mitigation solutions.
What are some common tools used to monitor and detect DDoS attacks?
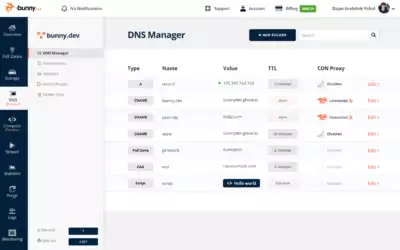
Some common tools include network traffic analyzers like Wireshark or tcpdump, intrusion detection and prevention systems (IDS/IPS), and dedicated DDoS detection and mitigation solutions like Arbor Networks or Cloudflare.
Can you provide any real-life examples of successful DDoS attack mitigation?
Sure! Here are a few examples:
– Company XYZ successfully mitigated a massive DDoS attack by using a combination of traffic scrubbing techniques and a cloud-based DDoS protection service.
– Organization ABC effectively detected and mitigated a DDoS attack by leveraging their in-house intrusion detection system and implementing rate limiting measures at their network edge.
– Website Z successfully defended against a DDoS attack by utilizing a content delivery network (CDN) with built-in DDoS protection capabilities.
How does traffic scrubbing help in mitigating DDoS attacks?
Traffic scrubbing involves analyzing incoming network traffic, identifying and filtering out malicious traffic, and only allowing legitimate traffic to reach the targeted network or service. It helps in mitigating DDoS attacks by filtering out the attack traffic and preventing it from overwhelming the target.
Can you explain rate limiting as a DDoS mitigation technique?
Rate limiting is a DDoS mitigation technique that involves placing limits on the number of requests or connections a source IP address can make within a specific time frame. By restricting the rate at which requests are accepted, it helps prevent the target from getting overloaded with excessive traffic.
What is the role of a content delivery network (CDN) in DDoS attack mitigation?
A content delivery network (CDN) can help in mitigating DDoS attacks by acting as a distributed network of servers that can absorb and distribute traffic. By spreading the load across multiple servers and employing various security measures, CDNs can help prevent DDoS attacks from overwhelming the target website or service.
Are there any other techniques or solutions for DDoS attack mitigation?
Yes, apart from traffic scrubbing, rate limiting, and CDNs, there are other techniques and solutions for DDoS attack mitigation. These can include using load balancers, implementing multi-layered security measures, employing behavioral analysis to detect anomalies, and leveraging machine learning algorithms for real-time threat detection and mitigation.