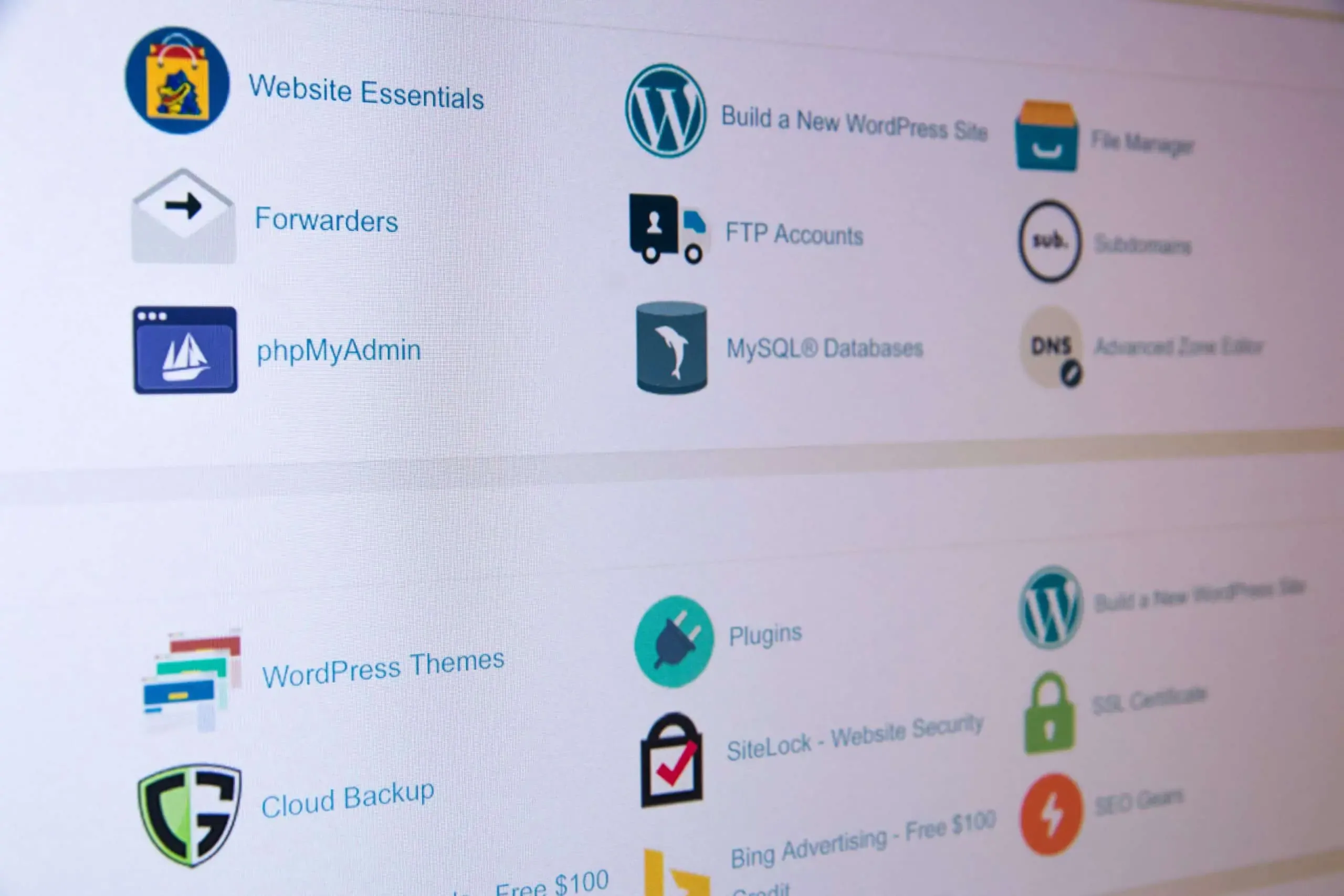
Understanding the Importance of cPanel Security
One cannot overlook the significance of cPanel security in today’s digital landscape. As cPanel serves as the control panel for managing websites, emails, and other services, ensuring its security is paramount. Effective cPanel security measures safeguard your hosting environment from potential threats and prevent unauthorized access to your server.
With the increasing number of cyber attacks and data breaches, investing in robust security measures is crucial. By implementing strong passwords and regularly updating them, you fortify your cPanel against brute force attacks. Furthermore, enabling two-factor authentication adds an extra layer of protection, requiring a second verification step for logins. Regularly updating and patching your cPanel is also essential to address any potential vulnerabilities and keep your system secure. Taking these measures minimizes the risk of malicious intrusions and ensures the safe and uninterrupted operation of your website.
The Role of Passwords in Securing Your cPanel
A strong and secure password is crucial for protecting your cPanel. It serves as the first line of defense against unauthorized access to your hosting environment. When creating a password, it is important to choose a combination of upper and lower case letters, numbers, and special characters. Avoid using easily guessable information such as your name, date of birth, or common words. Additionally, it is recommended to use a unique password for your cPanel that is not used for any other online accounts. Regularly changing your password further enhances the security of your cPanel and helps to prevent potential breaches.
Furthermore, it is essential to keep your password confidential. Sharing your cPanel password with others, even if they are trusted individuals, increases the risk of unauthorized access. It is best to create separate user accounts within cPanel for each person who requires access to your hosting environment. This ensures accountability and allows you to set different permission levels for each user. Periodically reviewing and updating the user accounts within your cPanel helps to minimize the potential for vulnerabilities and ensures that only authorized individuals have access to sensitive information.
Implementing Two-Factor Authentication for Enhanced Security
Two-factor authentication (2FA) is a powerful security measure that significantly enhances the protection of your cPanel. By implementing 2FA, you are adding an extra layer of defense that requires users to provide two forms of verification before accessing their accounts. This typically involves a combination of something they know, like a password, and something they have, like a unique code sent to their mobile device. With 2FA enabled, even if an attacker manages to obtain the user’s password, they still won’t be able to access the account without the additional verification.
The process of implementing 2FA for your cPanel is relatively straightforward. Most hosting providers offer built-in support for 2FA, and there are also third-party authentication services available. Once enabled, users will need to set up their 2FA method, usually by scanning a QR code or manually entering a secret key into an authentication app on their mobile device. From there, whenever they log in to their cPanel, they will be prompted to enter the unique code generated by the app, adding an extra layer of security to their account. By implementing 2FA, you are minimizing the risk of unauthorized access to your cPanel and safeguarding your sensitive data.
Regularly Updating and Patching cPanel for Vulnerability Fixes
Regularly updating and patching cPanel is crucial in ensuring the security and stability of your hosting environment. By keeping your cPanel software up to date, you can safeguard your website from potential vulnerabilities and exploits that could be exploited by hackers. Additionally, these updates often include bug fixes and performance enhancements, helping to improve the overall functionality and user experience of your cPanel interface.
To regularly update cPanel, you can simply enable automatic updates or manually check for updates through the cPanel interface. By staying on top of these updates and promptly applying them to your system, you can ensure that any security vulnerabilities are swiftly addressed and fixed, reducing the risk of unauthorized access and data breaches. Remember, the key to effective security lies not only in implementing preventive measures but also in regularly updating and patching your cPanel software to stay one step ahead of potential threats.
Protecting Your Hosting Environment through Firewall Configuration
Firewall configuration plays a crucial role in safeguarding your hosting environment from various cyber threats. By properly setting up and managing your firewall, you can establish a barrier that limits unauthorized access and protects your system from malicious activities.
One of the key aspects of firewall configuration is defining access rules and policies. By carefully configuring inbound and outbound traffic rules, you can control what types of connections are allowed or blocked. By explicitly specifying which IP addresses, ports, or protocols are permitted or denied, you can significantly reduce the risk of unauthorized access to your hosting environment. Additionally, regularly reviewing and updating these rules ensures that your firewall remains effective against emerging threats.
Enabling SSL/TLS Certificates for Secure Data Transmission
One of the essential measures for ensuring secure data transmission is enabling SSL/TLS certificates. SSL (Secure Sockets Layer) and its successor TLS (Transport Layer Security) are cryptographic protocols that establish a secure connection between a web server and a client. By encrypting the data transmitted between the two parties, SSL/TLS certificates help prevent unauthorized access and protect sensitive information from being intercepted.
Enabling SSL/TLS certificates involves obtaining a certificate from a trusted certificate authority (CA) and configuring it on your cPanel. Once installed, the SSL/TLS certificate adds an additional layer of protection to your website, displaying a padlock icon in the browser’s address bar and enabling the use of the HTTPS protocol. This ensures that any data transferred between the client and server remains encrypted and secure. By enabling SSL/TLS certificates, you can enhance the security of your website and build trust with your visitors, reassuring them that their information is protected during transmission.
Managing File and Directory Permissions to Prevent Unauthorized Access
When it comes to securing your cPanel, managing file and directory permissions plays a crucial role in preventing unauthorized access. By assigning appropriate permissions to files and directories, you can ensure that only authorized users have access to them.
Setting file and directory permissions involves granting or denying different levels of access to various users or groups. The three main permissions are read (r), write (w), and execute (x). By carefully configuring these permissions, you can control who can view, modify, and execute files and directories on your cPanel. It is essential to review and update these permissions regularly to maintain the security of your hosting environment and keep sensitive information protected from unauthorized individuals.
Implementing IP Whitelisting and Blacklisting for Added Security
IP whitelisting and blacklisting are crucial security measures that can help protect your cPanel and hosting environment from unauthorized access and potential threats. By implementing IP whitelisting, you are essentially creating a list of trusted IP addresses that are allowed to access your cPanel. This means that only the specified IP addresses will be able to access your cPanel, making it extremely difficult for anyone else to gain unauthorized entry. By restricting access to only a select few trusted IPs, you can significantly reduce the risk of malicious attacks and unauthorized access to your sensitive data.
On the other hand, IP blacklisting involves identifying and blocking specific IP addresses that are known to be malicious or pose a threat to your cPanel’s security. This proactive approach helps to prevent any potential attacks from these IP addresses by automatically blocking their access. By regularly updating and maintaining a comprehensive blacklist, you can ensure that any known malicious IP addresses are effectively blocked, adding an extra layer of security to your cPanel. Implementing both IP whitelisting and blacklisting can provide you with enhanced control over who can access your cPanel and significantly minimize the risk of unauthorized access and potential security breaches.
Regularly Monitoring and Logging cPanel Activities
Regularly monitoring and logging cPanel activities is a crucial aspect of maintaining a secure hosting environment. By consistently monitoring the activities within cPanel, you can stay vigilant and detect any suspicious or unauthorized actions promptly. This proactive approach allows you to respond swiftly and effectively, minimizing the potential damage that security breaches can cause.
One of the primary benefits of logging cPanel activities is the ability to review and analyze the data for any signs of irregularities or suspicious behavior. By examining the log files regularly, you can identify any unauthorized attempts to access your cPanel, unusual login patterns, or unauthorized changes to settings. This not only helps in ensuring the security of your hosting environment but also aids in investigating any potential security incidents. Moreover, logging cPanel activities enables you to track the usage of system resources and helps in identifying any performance issues that may arise.
Utilizing Backup and Restore Features to Safeguard Your Hosting Environment
One essential practice in ensuring the security of your hosting environment is to utilize backup and restore features. These features provide a reliable and effective way to safeguard your data and website in case of unexpected events or accidents. By regularly backing up your files, databases, and configurations, you can minimize the risk of losing significant data or facing lengthy downtime. In the event of a security breach or system failure, having a recent backup allows you to restore your website and get it up and running quickly. It is recommended to establish a backup schedule that suits your needs and preferences, whether it is daily, weekly, or monthly, to ensure that you always have an up-to-date copy of your website. Additionally, it is crucial to store your backups in a secure location, such as an offsite server or cloud storage, to prevent potential data loss due to physical hardware failures or disasters. By implementing a solid backup and restore strategy, you can significantly enhance the security and resilience of your hosting environment.
What is cPanel security and why is it important?
cPanel security refers to the measures taken to protect the hosting environment powered by cPanel. It is important because it helps prevent unauthorized access, data breaches, and potential damage to your website and server.
How does using strong passwords contribute to securing my cPanel?
Strong passwords are harder to guess or crack, reducing the risk of unauthorized access to your cPanel. They act as the first line of defense against potential security threats.
What is two-factor authentication and why should I enable it for my cPanel?
Two-factor authentication adds an extra layer of security by requiring a second verification step, typically a unique code sent to your mobile device. Enabling it enhances the security of your cPanel by making it significantly more difficult for unauthorized individuals to gain access.
Why is it important to regularly update and patch cPanel?
Regular updates and patches help fix vulnerabilities and security issues in cPanel. By keeping your cPanel up to date, you ensure that any known security flaws are patched, reducing the risk of a security breach.
How does firewall configuration protect my hosting environment?
Firewall configuration filters network traffic and blocks unauthorized access attempts, reducing the risk of malicious attacks and unauthorized access to your hosting environment.
What are SSL/TLS certificates and why should I enable them for secure data transmission?
SSL/TLS certificates encrypt data transmitted between the users’ browsers and your server, ensuring that sensitive information remains secure and protected from interception by unauthorized individuals.
How do file and directory permissions prevent unauthorized access?
File and directory permissions determine who can read, write, or execute files and directories. By setting appropriate permissions, you can limit access to sensitive files and prevent unauthorized users from modifying or accessing them.
What is IP whitelisting and blacklisting, and how do they enhance security?
IP whitelisting allows only specific IP addresses to access your cPanel, while blacklisting blocks specific IP addresses from accessing it. By implementing these measures, you can restrict access to your cPanel to trusted users and block potentially malicious IP addresses.
Why is it important to regularly monitor and log cPanel activities?
Regular monitoring and logging of cPanel activities allow you to track any suspicious or unauthorized actions. It helps in identifying security breaches, detecting potential threats, and taking necessary actions to mitigate them.
How does utilizing backup and restore features safeguard my hosting environment?
By regularly backing up your hosting environment, you ensure that you have copies of your data in case of accidental data loss, hardware failure, or security breaches. The ability to restore your hosting environment from these backups provides an added layer of protection for your website and server.