The Importance of Email Security
Email has become an integral part of our daily lives, serving as a primary means of communication for both personal and business purposes. However, with its widespread usage, the importance of email security cannot be overstated. Cybercriminals are constantly developing new tactics to exploit vulnerabilities within email systems, making it crucial for individuals and organizations to prioritize the security of their email communications.
A breach in email security can have far-reaching consequences, ranging from unauthorized access to sensitive data and financial information to the spread of malware and phishing attacks. Personal information, such as passwords, social security numbers, and banking details, can be compromised, leading to identity theft and financial loss. Furthermore, businesses can suffer reputational damage, legal issues, and financial repercussions if their email systems are compromised. As such, implementing robust email security measures is not just a matter of convenience but a necessity in today’s digital landscape.
Understanding Email Authentication
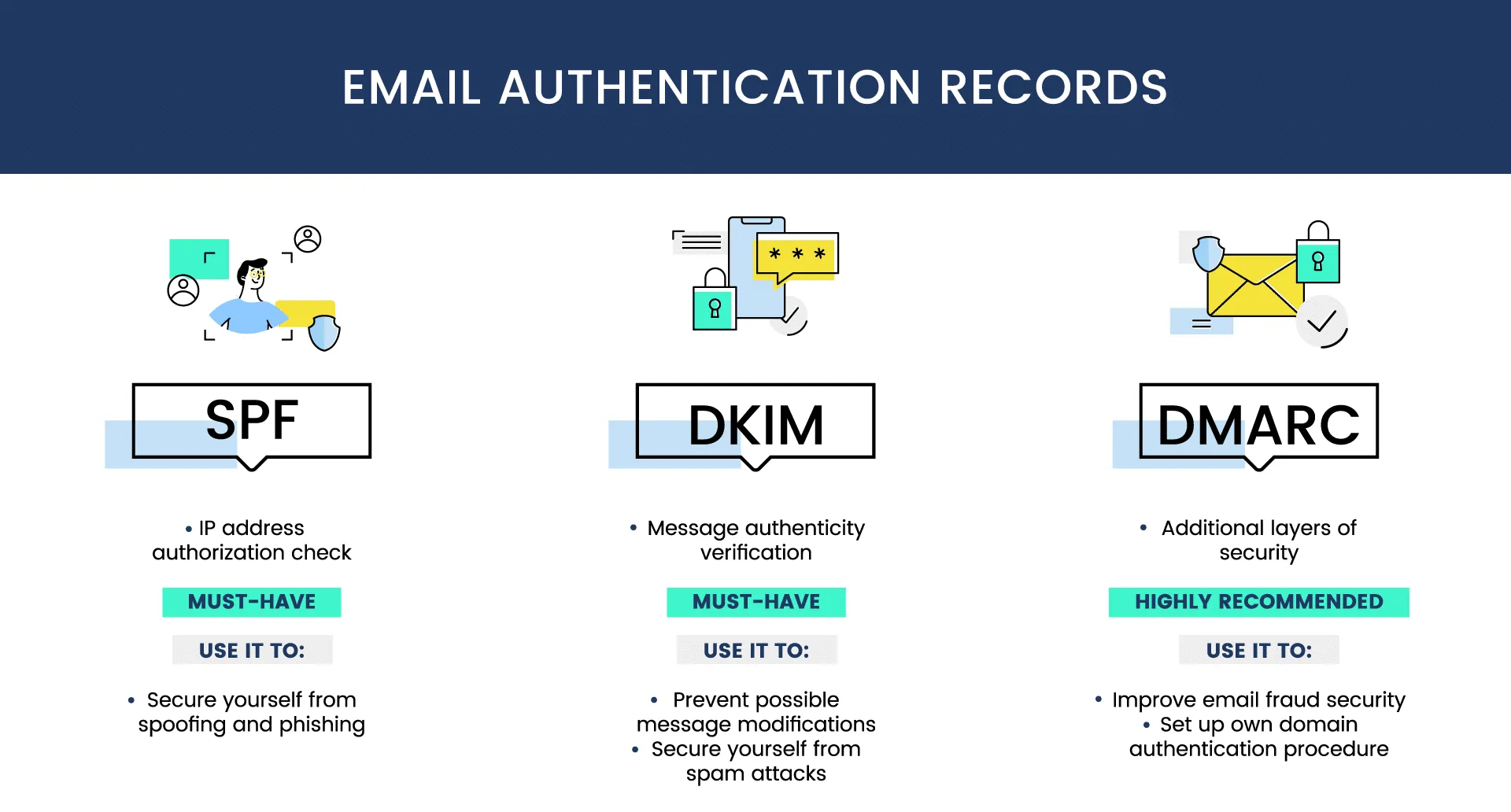
Email authentication is a crucial aspect of email security that helps verify the authenticity of messages. It ensures that the sender of an email is who they claim to be, thereby reducing the risk of unauthorized or forged emails. By implementing email authentication protocols, organizations can effectively protect their email systems and prevent spam, phishing attacks, and other malicious activities.
One key component of email authentication is the Sender Policy Framework (SPF). SPF allows domain owners to specify which servers are authorized to send emails on their behalf. When an email is received, the recipient’s server can check the SPF record of the sender’s domain to confirm if the email is sent from an authorized server. SPF helps prevent email spoofing and ensures that only legitimate emails from authorized servers are delivered.
The Role of SPF in Email Security
Sender Policy Framework (SPF) plays a crucial role in ensuring email security. With the increasing prevalence of email spam and phishing attacks, it has become essential for businesses and individuals to protect their email communications. SPF is a protocol that helps prevent email spoofing by verifying the sender’s identity.
By defining a set of authorized email servers that are allowed to send emails on behalf of a domain, SPF enables the recipient’s mail server to check if the incoming email is originating from an authorized source. This verification process helps in identifying and blocking emails that are sent from unauthorized servers, thereby reducing the risk of email forgery and impersonation. SPF acts as a shield against email spoofing attacks, ensuring that only legitimate emails are delivered to the recipient’s inbox.
Implementing SPF records in the Domain Name System (DNS) of a domain involves specifying the authorized email servers’ IP addresses. When an email is received, the SPF record is queried to confirm if the email server IP address matches the authorized sources mentioned in the DNS record. If the verification fails, the recipient’s email server can take appropriate action to handle the email, such as marking it as spam or rejecting it altogether. By incorporating SPF into their email security practices, organizations can significantly enhance their defense against phishing attacks and protect their email infrastructure from being exploited by malicious actors.
How DKIM Enhances Email Authentication
DKIM (DomainKeys Identified Mail) plays a vital role in enhancing email authentication. It provides a way to verify the integrity and authenticity of email messages, ensuring that they have not been tampered with during transit. By using cryptographic signatures, DKIM allows the recipient’s mail server to verify that the email was indeed sent by the claimed sender and that its content remains intact.
When an email is sent, the sender’s mail server applies a unique DKIM signature to the outgoing message. This signature is generated using a private key that is securely stored by the sender. Upon receiving the email, the recipient’s mail server can then retrieve the public key from the sender’s DNS record and use it to verify the DKIM signature. If the signature is valid and matches the email’s content, the recipient can be confident of the email’s authenticity. DKIM provides an additional layer of security for email communication, helping to prevent spam, spoofing, and phishing attempts.
DMARC: Strengthening Email Security Measures
DMARC, which stands for Domain-based Message Authentication, Reporting, and Conformance, plays a vital role in strengthening email security measures. By combining the benefits of SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail), DMARC provides a comprehensive solution to verify the authenticity of email messages.
One of the key advantages of DMARC is its ability to protect against email spoofing and phishing attacks. By implementing strict policies, organizations can ensure that only legitimate emails from authorized senders are delivered to their recipients. Additionally, DMARC provides valuable insights and reporting capabilities, allowing businesses to monitor email activity and identify any suspicious or unauthorized email senders. With the growing sophistication of cyber threats, DMARC is an essential tool that enhances email security and protects both individuals and organizations from potential breaches.
Configuring SPF Records for Email Protection
One crucial aspect of email security is configuring SPF records. SPF, which stands for Sender Policy Framework, is a method used to prevent email spoofing and phishing attacks. By creating SPF records, you can specify which servers are allowed to send emails on behalf of your domain. This helps to establish a verification system that enables email receivers to determine the authenticity of the email sender.
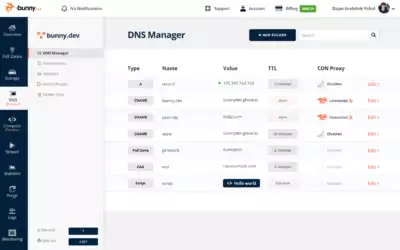
To configure SPF records, you need to know the specific syntax for creating the records in your domain’s DNS settings. Typically, you will need to add a TXT record with the SPF information, specifying the IP addresses or hostnames of the servers authorized to send emails for your domain. It is essential to carefully follow the correct format and syntax to ensure the SPF records are properly set up. By correctly configuring SPF records, you can enhance email security and reduce the risk of unauthorized emails being sent on behalf of your domain.
Implementing DKIM Signatures for Email Verification
DKIM (DomainKeys Identified Mail) is a widely-used email authentication method designed to verify the authenticity of emails. By implementing DKIM signatures for email verification, organizations can add an extra layer of security to their email communication.
To implement DKIM, organizations need to generate a pair of cryptographic keys – a private key and a public key. The private key is kept secure within the organization’s email server, while the public key is published in the Domain Name System (DNS) record. When an email is sent from the organization’s domain, the email server adds a digital signature created using the private key. Recipient servers can then use the public key to validate the signature and verify that the email is genuine and has not been altered in transit. This ensures that the email can be trusted and increases the chances of message delivery.
• DKIM (DomainKeys Identified Mail) is an email authentication method used for verifying the authenticity of emails.
• Implementing DKIM signatures adds an extra layer of security to email communication.
• To implement DKIM, organizations need to generate a private key and a public key pair.
• The private key is kept secure within the organization’s email server.
• The public key is published in the Domain Name System (DNS) record.
• When an email is sent from the organization’s domain, the email server adds a digital signature using the private key.
• Recipient servers can use the public key to validate the signature and verify that the email has not been altered during transit.
• This process ensures that emails can be trusted and increases message delivery reliability.
Setting Up DMARC Policies for Enhanced Email Security
DMARC (Domain-based Message Authentication, Reporting, and Conformance) policies play a crucial role in enhancing email security by preventing email spoofing and phishing attacks. By implementing DMARC policies, organizations can ensure that their email messages are authenticated and delivered securely to recipients. To set up DMARC policies, organizations need to follow a few essential steps.
Firstly, organizations need to enable DMARC by adding a DMARC record to their DNS (Domain Name System) configuration. This record allows the organization to specify the DMARC policy mode, such as monitoring, quarantine, or reject. In monitoring mode, organizations receive detailed reports about the alignment of their outgoing email messages, helping them gain insights into potential issues and threats. Quarantine and reject modes provide more stringent protection by instructing receiving email servers to either deliver suspicious messages to the spam folder or reject them outright. By selecting an appropriate policy mode, organizations can ensure that only legitimate emails reach their intended recipients, enhancing their overall email security. Additionally, organizations should regularly monitor their DMARC reports and analyze any issues or failed authentications to refine their policies and strengthen their email security measures.
Best Practices for Email Security with BunnyCDN
Email security is of paramount importance in today’s digital landscape. With the increasing number of cyber threats and scams, it is crucial to implement best practices to ensure the safety and integrity of email communication. BunnyCDN, a well-known content delivery network, offers effective solutions for enhancing email security.
One key best practice is to configure SPF (Sender Policy Framework) records for email protection. SPF helps prevent email spoofing by verifying that the sender’s IP address is authorized to send emails on behalf of a domain. By setting up SPF records correctly, you can significantly reduce the risk of phishing attacks and ensure that only legitimate emails are delivered. BunnyCDN provides a user-friendly interface to configure SPF records effectively, making it easier to implement this essential security measure.
Another important practice is to implement DKIM (DomainKeys Identified Mail) signatures for email verification. DKIM adds a digital signature to outgoing emails, allowing the recipient to verify the email’s authenticity. This verification process ensures that the email has not been tampered with during transmission. BunnyCDN offers a seamless integration of DKIM signatures, allowing you to easily add an extra layer of security to your email communication. By implementing DKIM, you can establish trust and reduce the risk of email fraud.
Common Challenges in Email Authentication
One of the common challenges in email authentication is the lack of proper implementation of SPF (Sender Policy Framework) records. SPF helps to authenticate the sender’s identity by allowing recipients to verify that the email is coming from an authorized source. However, many organizations fail to configure SPF records correctly, leading to failed email delivery or potential security breaches.
Another challenge is the incorrect setup of DKIM (DomainKeys Identified Mail) signatures. DKIM adds a digital signature to outgoing emails, ensuring their authenticity. However, if DKIM keys are not generated or implemented correctly, it may result in failed email authentication or even rejection by recipient servers. This can often be a technical hurdle for organizations, as it requires proper configuration and maintenance of DKIM keys for multiple domains and email senders.
Benefits of Using BunnyCDN for Email Security
BunnyCDN offers several benefits for enhancing email security. Firstly, BunnyCDN’s global network ensures that emails are delivered quickly and securely all over the world. With servers strategically located in various regions, BunnyCDN allows for efficient delivery of emails, reducing the chances of latency and ensuring that messages reach recipients promptly.
In addition, BunnyCDN provides robust protection against email spoofing and phishing attacks. By implementing advanced email authentication mechanisms such as SPF, DKIM, and DMARC, BunnyCDN helps verify the authenticity of emails before delivery. This prevents malicious actors from impersonating legitimate senders and helps ensure that recipients only receive genuine and trusted emails. With BunnyCDN’s comprehensive email security measures, businesses can enhance their brand reputation, protect sensitive information, and provide a secure communication channel for their customers.
Integrating BunnyCDN with Email Service Providers
Email service providers play a crucial role in ensuring the delivery and security of emails. When it comes to integrating BunnyCDN with email service providers, it can offer significant benefits in terms of enhancing email security. By leveraging BunnyCDN’s robust infrastructure and advanced features, email service providers can improve their overall email delivery rates while effectively protecting against various types of cyber threats.
One of the key advantages of integrating BunnyCDN with email service providers is the capability to implement SPF, DKIM, and DMARC protocols seamlessly. These protocols play a vital role in email authentication and security. BunnyCDN offers straightforward configuration options for SPF records, enabling email service providers to verify the authenticity of outgoing emails and prevent domain spoofing. With DKIM signatures, BunnyCDN ensures that emails are properly signed, protecting them from tampering during transit. Additionally, BunnyCDN allows the setting up of DMARC policies, helping email service providers fortify their security measures and effectively combat email phishing and spoofing attacks. By integrating BunnyCDN with email service providers, organizations can enhance their email security while maintaining efficient email delivery.
Future Trends in Email Security
Future Trends in Email Security
With the ever-increasing volume of cyber threats, the email security landscape is constantly evolving to stay one step ahead. One of the future trends in email security is the adoption of advanced machine learning algorithms. Machine learning can analyze large amounts of data and detect patterns that may be indicators of phishing attempts or other malicious activities. By continuously learning and adapting to new threats, these algorithms can enhance the effectiveness of email filtering and provide better protection against sophisticated attacks.
Another emerging trend is the use of behavioral analytics in email security. Unlike traditional methods that rely on predefined rules, behavioral analytics analyze the behavior of users and devices to identify anomalies. By establishing a baseline of normal behavior, any deviation from it can trigger an alert for further investigation. This approach can detect new and unknown threats that may not be captured by traditional signature-based methods. Additionally, behavioral analytics can provide insights into user habits and patterns, helping organizations identify potential security training needs or insider threats.
As email continues to be a primary communication channel for individuals and businesses, staying ahead of email security threats is crucial. By embracing advanced machine learning algorithms and behavioral analytics, organizations can strengthen their email security measures and better protect sensitive information from falling into the wrong hands.
Why is email security important?
Email security is crucial because it helps protect sensitive information from being accessed, intercepted, or manipulated by unauthorized individuals. It ensures data confidentiality, integrity, and authenticity.
What is email authentication?
Email authentication is the process of verifying the origin and integrity of an email message. It helps determine whether an email is legitimate or forged by checking its digital signature or verifying the sending server’s identity.
What is the role of SPF in email security?
SPF (Sender Policy Framework) is an email authentication method that helps prevent email spoofing and forgery. It verifies that the sending server is authorized to send emails on behalf of a specific domain, reducing the chances of fraudulent emails reaching recipients.
How does DKIM enhance email authentication?
DKIM (DomainKeys Identified Mail) adds an encrypted digital signature to email messages, allowing recipients to verify the email’s integrity and confirm that it hasn’t been tampered with during transit. It enhances email authentication and helps prevent email spoofing and phishing attacks.
What is DMARC, and how does it strengthen email security measures?
DMARC (Domain-based Message Authentication, Reporting, and Conformance) is an email authentication protocol that combines SPF and DKIM. It enables domain owners to specify how email servers should handle unauthenticated emails, reducing the risk of email fraud and improving email deliverability.
How do you configure SPF records for email protection?
Configuring SPF records involves adding a DNS TXT record to your domain’s DNS settings. This record specifies the authorized email servers that can send emails on behalf of your domain. By properly configuring SPF, you can enhance email security and prevent email spoofing.
How do you implement DKIM signatures for email verification?
Implementing DKIM involves generating a public-private key pair for your domain and adding a DNS TXT record. The private key is used to sign outgoing emails, while the public key is published in the DNS record. This allows recipients to verify the email’s authenticity and integrity.
How can you set up DMARC policies for enhanced email security?
To set up DMARC, you need to publish a DMARC TXT record in your domain’s DNS settings. This record specifies the email handling policies, such as whether to reject or quarantine unauthenticated emails. By implementing DMARC policies, you can strengthen your email security measures.
What are the best practices for email security with BunnyCDN?
Some best practices for email security with BunnyCDN include enabling SPF, DKIM, and DMARC for your domain, regularly monitoring email authentication reports, configuring strict DMARC policies, and integrating BunnyCDN with your email service providers.
What are the common challenges in email authentication?
Common challenges in email authentication include misconfigured SPF or DKIM records, inconsistent implementation across different email service providers, lack of visibility into email authentication failures, and the complexity of managing multiple domains and subdomains.
How does using BunnyCDN benefit email security?
Using BunnyCDN for email security provides benefits such as improved email deliverability, reduced email fraud and phishing attacks, enhanced brand reputation, increased recipient trust, and simplified management of email authentication protocols.
How can BunnyCDN be integrated with email service providers?
BunnyCDN can be integrated with email service providers by following their specific instructions to configure SPF, DKIM, and DMARC records. This integration ensures that emails sent through the email service provider are authenticated and protected by BunnyCDN’s email security features.
What are the future trends in email security?
Future trends in email security may include advancements in machine learning and artificial intelligence to detect and prevent sophisticated email threats, increased adoption of stronger encryption methods, improved user awareness and education about email security, and tighter integration between email service providers and security solutions.