API Endpoint Security: An Overview
API Endpoint Security is a critical aspect of any organization’s overall security strategy. As the bridge between the outside world and internal systems, API endpoints are attractive targets for malicious actors seeking to gain unauthorized access or exploit vulnerabilities. Therefore, ensuring the security of these endpoints is of paramount importance.
API endpoint security encompasses a wide range of measures aimed at protecting API endpoints from both external and internal threats. This includes implementing strong authentication mechanisms to verify the identity of users accessing the endpoints, as well as controlling access to ensure that only authorized individuals or systems are granted permission. Additionally, securing API endpoints involves implementing robust encryption and data protection measures to safeguard the confidentiality and integrity of the data being transmitted. By taking a comprehensive approach to API endpoint security, organizations can mitigate the risks associated with unauthorized access, data breaches, and other potential security incidents.
Understanding Cloudflare Access Policies
Cloudflare Access Policies provide a secure way to restrict access to your API endpoints. These policies allow you to define specific rules and conditions for who can access your endpoints. By implementing Access Policies, you can ensure that only authorized users or systems can interact with your APIs, thus minimizing the risk of data breaches or unauthorized access.
One key feature of Cloudflare Access Policies is the ability to set granular access controls based on user identity or IP address. This means that you can define rules that allow access only to specific users or groups, or restrict access based on the IP address of the user. This level of control ensures that only authenticated and authorized individuals can access your API endpoints, adding an extra layer of security to your applications. Additionally, Access Policies provide detailed logging and auditing capabilities, allowing you to track and monitor access attempts, identify potential security threats, and ensure compliance with your organization’s security standards.
The Importance of Securing API Endpoints
Securing API endpoints is of utmost importance in today’s digital landscape. With the increasing reliance on APIs for seamless integration between systems and applications, ensuring the security of these endpoints has become a critical concern for businesses. Failing to adequately secure API endpoints can leave organizations vulnerable to a wide range of cyber threats and attacks, jeopardizing the integrity and confidentiality of their data.
One key aspect of securing API endpoints is protecting sensitive user information. APIs often handle sensitive data such as personal information, authentication credentials, and financial details. If these endpoints are not properly secured, hackers can exploit vulnerabilities to gain unauthorized access and steal or manipulate this sensitive information. This can lead to serious consequences, including identity theft, financial loss, and damage to an organization’s reputation. Therefore, implementing robust security measures for API endpoints is essential to safeguard sensitive data and maintain the trust of users.
Exploring the Threat Landscape for API Endpoints
API endpoints have become an integral part of modern applications, allowing them to communicate and share data with other systems. However, this increased connectivity also brings with it a heightened risk of security threats. As organizations increasingly rely on APIs to drive their business processes, it is crucial to explore the threat landscape to understand the potential vulnerabilities that can be exploited.
One common threat is the attack on the authentication and authorization mechanisms implemented for API endpoints. Hackers may attempt to gain unauthorized access to sensitive data by bypassing these security measures. Another significant threat is the exposure of sensitive information through API endpoints. If proper data validation and access controls are not in place, malicious actors can exploit vulnerabilities to extract sensitive information, leading to serious consequences such as data breaches or identity theft. Understanding these potential threats is essential in establishing a robust security framework for API endpoints.
Common Vulnerabilities in API Endpoints
API endpoints are a crucial component of any modern web application. They enable the exchange of data and functionality between different systems. However, with this convenience comes the potential for vulnerabilities that can be exploited by malicious actors. One common vulnerability in API endpoints is improper input validation. When input parameters are not appropriately validated, it opens the door for attackers to manipulate requests and potentially gain unauthorized access to sensitive data or execute unintended actions.
Another significant vulnerability is insufficient authorization and authentication mechanisms. Without adequate controls in place, unauthorized users may be able to access or manipulate data through API endpoints. This can lead to data breaches, unauthorized modifications, and other security incidents. It is essential to implement strong access controls, such as authentication tokens or API keys, to ensure that only authorized users can access and interact with API endpoints.
Additionally, developers should also be mindful of potential security vulnerabilities such as insecure direct object references, cross-site scripting (XSS) attacks, and SQL injection. These types of vulnerabilities can allow attackers to bypass security measures and gain unauthorized access to data or execute arbitrary code. Regular security assessments, threat modeling, and code reviews can help identify and address these vulnerabilities in API endpoints.
In the next section, we will delve into how Cloudflare Access Policies can help address and mitigate some of the common vulnerabilities in API endpoints.
Introducing Cloudflare Access Policies
Cloudflare Access Policies provide a secure solution for managing and controlling access to API endpoints. With Access Policies, organizations can ensure that only authorized users and devices can reach their APIs. This helps in preventing unauthorized access and protects sensitive data from potential attacks or breaches.
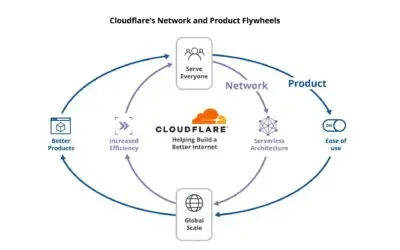
Access Policies work by allowing organizations to set up rules and conditions to control who can access API endpoints. These policies can be based on a variety of factors such as user identity, device type, or network location. By establishing granular access controls, organizations can customize and enforce specific security measures for their API endpoints. With Cloudflare Access Policies, organizations can strengthen their security posture and mitigate potential risks associated with unauthorized access to API endpoints.
How Cloudflare Access Policies Work
Cloudflare Access Policies provide a reliable way to control access to API endpoints. These policies work by leveraging Cloudflare’s network infrastructure to act as a gateway between the client and the API endpoint. When a request is made to access the API, Cloudflare verifies the user’s identity based on a set of predefined rules and policies.
Access policies can be set up to include a variety of authentication methods, such as single sign-on (SSO), password-based authentication, or integration with external identity providers. Once a user’s identity is verified, Cloudflare applies the appropriate access controls, allowing or denying access based on the defined policies. This way, only authorized users or entities can interact with the API endpoints, significantly reducing the risk of unauthorized access and potential security breaches. By implementing and configuring Cloudflare Access Policies, organizations can ensure that their API endpoints are secure and accessed only by the intended users or entities.
Setting Up Access Policies for API Endpoints
Access policies play a crucial role in ensuring the security of API endpoints. To set up access policies for API endpoints, organizations need to first determine the level of access they want to grant. This involves identifying the groups or individuals who should have access to specific endpoints and the type of access they should be granted. Once this is determined, organizations can use tools like Cloudflare Access Policies to define and enforce these access rules.
When setting up access policies, it is essential to consider the principle of least privilege. This means granting only the minimal level of access necessary for an individual or group to perform their intended functions. By following this principle, organizations can reduce the risk of unauthorized access and potential breaches. Additionally, regularly reviewing and updating access policies is crucial to ensure that they align with any changes in user roles or responsibilities within the organization. Properly configuring access policies allows organizations to maintain control over their API endpoints and strengthen their overall security posture.
Best Practices for Configuring Cloudflare Access Policies
When it comes to configuring Cloudflare Access Policies for API endpoints, there are several best practices that should be followed to ensure maximum security. Firstly, it is important to carefully define and restrict the access permissions granted to users or groups. By implementing a least privilege approach, where users are only given the minimum access necessary to perform their tasks, the risk of unauthorized access or data breaches can be minimized. Additionally, regularly reviewing and updating access policies is crucial to adapt to any changes in user roles or responsibilities, as well as to promptly revoke access for users who no longer require it.
Another important aspect of configuring Cloudflare Access Policies is to leverage the principle of defense in depth. This involves implementing multiple layers of security controls to protect API endpoints. For example, in addition to Cloudflare Access, other security measures such as strong authentication mechanisms and IP whitelisting can be used to strengthen the overall security posture. By combining these different security controls, the likelihood of unauthorized access or malicious activities is greatly reduced. It is also recommended to regularly monitor and analyze access logs to detect any suspicious activities and take appropriate actions to mitigate potential threats.
Implementing Multi-Factor Authentication for API Endpoints
Multi-factor authentication (MFA) is a crucial measure for enhancing the security of API endpoints. By requiring users to provide multiple forms of identification, MFA adds an extra layer of protection against unauthorized access and potential data breaches. One commonly used MFA method is the combination of a password and a verification code sent to a user’s mobile device. This ensures that even if an attacker manages to obtain a user’s password, they would still require physical access to the user’s mobile device to complete the authentication process.
To implement MFA for API endpoints, organizations can leverage various authentication protocols such as OAuth, OpenID Connect, or SAML. These protocols enable the integration of MFA capabilities into the authentication flow, allowing organizations to enforce additional verification steps before granting access to API endpoints. Moreover, using APIs provided by authentication providers or identity management platforms, developers can easily incorporate MFA into their existing systems, without the need for extensive code modifications. By implementing MFA for API endpoints, organizations can significantly reduce the risk of unauthorized access, mitigate the impact of credential theft, and ensure the confidentiality and integrity of critical data.
Monitoring and Logging Access to API Endpoints
API endpoints are critical components of any application, and it is crucial to have visibility into who is accessing them and when. Monitoring access to API endpoints involves tracking and recording all incoming requests, including information such as the IP addresses, user agents, and timestamps. By maintaining a comprehensive log of API access, organizations can identify any suspicious or malicious activity and take necessary action to mitigate potential security threats.
In addition to monitoring access, logging plays a vital role in API endpoint security. Logs provide a detailed record of every API interaction, capturing essential information that can be used for troubleshooting, auditing, and forensic analysis. Logging access to API endpoints allows organizations to review the specifics of each request, including the endpoints accessed, the data transmitted, and any errors or exceptions encountered. With comprehensive and well-structured logs, organizations can have a reliable audit trail that helps in identifying any unauthorized access, compliance violations, or abnormal behavior.
Testing and Auditing API Endpoint Security
Testing and auditing API endpoint security is crucial in order to identify vulnerabilities and ensure the integrity of the system. By conducting thorough testing, organizations can detect any weaknesses or flaws in their API endpoints, allowing them to address these issues before they can be exploited by attackers. This involves a comprehensive assessment of the endpoint’s security controls, such as authentication mechanisms, input validation, and encryption protocols. Through rigorous testing, organizations can determine the effectiveness of their security measures and make necessary adjustments to strengthen the overall security posture of their API endpoints.
Auditing API endpoint security is equally important, as it provides a means to monitor and evaluate the effectiveness of the security controls in place. This involves reviewing access logs, analyzing security event data, and examining configuration settings to ensure they align with industry best practices. Regular audits enable organizations to stay informed about any changes in the threat landscape and to identify potential security gaps or vulnerabilities that may have emerged over time. By conducting routine audits, organizations can maintain the integrity and confidentiality of their data and ensure compliance with relevant security standards.
Ensuring Compliance with API Endpoint Security Standards
Developing and implementing robust security standards for API endpoints is crucial in ensuring compliance with industry regulations and safeguarding sensitive data. API endpoint security standards provide a set of guidelines and best practices that organizations must adhere to, in order to protect their APIs from potential threats and vulnerabilities. These standards cover various aspects such as authentication, authorization, encryption, and data privacy.
To ensure compliance with API endpoint security standards, organizations should establish a comprehensive security framework that includes regular risk assessments, vulnerability scanning, and penetration testing. This will help identify any potential weaknesses or gaps in the security infrastructure and allow for prompt remediation. Additionally, organizations should regularly review and update their security policies and procedures to adapt to new threats and evolving compliance requirements. By diligently following these security standards, organizations can maintain the integrity and confidentiality of their API endpoints and mitigate the risks associated with unauthorized access or data breaches.
What is API endpoint security?
API endpoint security refers to the measures taken to protect the endpoints of an API (Application Programming Interface) from unauthorized access, data breaches, and other security threats.
What are Cloudflare Access policies?
Cloudflare Access policies are a feature provided by Cloudflare that allow administrators to control who can access their API endpoints. By setting up access policies, administrators can ensure that only authorized users can interact with their APIs.
Why is securing API endpoints important?
Securing API endpoints is crucial because they serve as a gateway to sensitive data and resources. Without proper security measures, API endpoints can be exploited by attackers to gain unauthorized access, manipulate data, or disrupt services.
What are some common vulnerabilities in API endpoints?
Common vulnerabilities in API endpoints include insufficient authentication and authorization mechanisms, lack of input validation, insecure direct object references, and exposure of sensitive data through error messages.
How do Cloudflare Access policies work?
Cloudflare Access policies work by intercepting requests to API endpoints and verifying the identity of the user making the request. Only users who meet the defined access policy criteria, such as possessing valid credentials or being part of a specific group, will be granted access.
How can I set up access policies for API endpoints with Cloudflare?
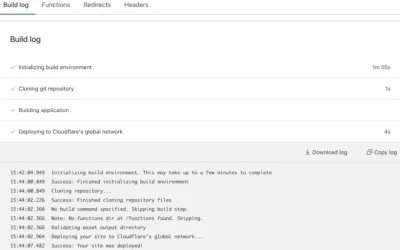
To set up access policies for API endpoints with Cloudflare, you need to configure the desired access rules and criteria using Cloudflare’s dashboard or API. This involves specifying the allowed users, their authentication methods, and the conditions for granting access.
What are some best practices for configuring Cloudflare Access policies?
Some best practices for configuring Cloudflare Access policies include implementing the principle of least privilege, regularly reviewing and updating access policies, using strong authentication methods like multi-factor authentication, and monitoring access logs for any suspicious activity.
How can I implement multi-factor authentication for API endpoints?
You can implement multi-factor authentication for API endpoints by enabling and configuring it within Cloudflare Access policies. This typically involves requiring users to provide a combination of something they know (e.g., a password) and something they possess (e.g., a time-based one-time password generated by a mobile app).
How can I monitor and log access to API endpoints?
You can monitor and log access to API endpoints by enabling Cloudflare’s logging feature and integrating it with a logging service or SIEM (Security Information and Event Management) system. This allows you to track and analyze access events, detect anomalies, and investigate any potential security incidents.
How should I test and audit API endpoint security?
To test and audit API endpoint security, you should conduct regular penetration tests, vulnerability assessments, and code reviews. Additionally, you can perform security audits to ensure compliance with industry standards and best practices.
How can I ensure compliance with API endpoint security standards?
To ensure compliance with API endpoint security standards, you should regularly review and update your security measures, stay informed about the latest security threats and best practices, and follow industry-specific standards and regulations applicable to your organization.