Cloudflare Firewall: Understanding the Basics
Cloudflare Firewall is a vital component of website security, designed to protect websites from various online threats. It acts as a barrier between the website and potential threats, filtering out malicious traffic and minimizing the risk of attacks. Essentially, it serves as the first line of defense, intercepting requests and analyzing them before they reach the website’s server.
The Firewall operates at the DNS level, meaning that it can block potentially harmful traffic before it even reaches the website. It uses a combination of predetermined rules, as well as customizable ones, to identify and block suspicious or malicious requests. These rules can be based on IP addresses, user agents, countries, or specific patterns of requests. By implementing the Cloudflare Firewall, website owners can enhance their security posture and significantly reduce the chances of falling victim to common cyber threats.
Exploring the Importance of WordPress Security
WordPress is one of the most popular content management systems (CMS) in the world, powering millions of websites. However, its popularity also makes it a prime target for hackers and malicious actors. This is why ensuring the security of your WordPress website is of utmost importance.
Security breaches can have severe consequences, ranging from data theft and website defacement to loss of customer trust and damaged reputation. Without adequate security measures in place, your WordPress site is vulnerable to a wide array of threats, such as brute force attacks, SQL injection attacks, and distributed denial-of-service (DDoS) attacks. Therefore, it is crucial to understand the importance of WordPress security and take proactive steps to protect your website.
Common Threats to WordPress Websites
WordPress websites are highly popular, making them a prime target for various types of threats. One common threat is malware infections. Malware can infiltrate WordPress websites through vulnerable plugins, themes, or even weak passwords. Once infected, the malware can wreak havoc by redirecting visitors to malicious websites, injecting unwanted ads, or stealing sensitive information from users and website owners alike.
Another significant threat to WordPress websites is brute force attacks. In these attacks, hackers attempt to systematically guess the correct username and password combination to gain unauthorized access to the website’s admin area. These attacks are usually automated, with hackers using specialized software to make numerous login attempts within a short period. Successful brute force attacks can lead to compromised websites, stolen data, defacement, or even complete loss of control over the website.
The Role of Cloudflare Firewall in WordPress Security
WordPress is a popular platform for website development, but it is not immune to security vulnerabilities. Hackers often exploit these weaknesses to gain unauthorized access, deface websites, or steal sensitive data. This is where the Cloudflare Firewall plays a crucial role in enhancing WordPress security.
The Cloudflare Firewall provides an additional layer of protection by filtering incoming traffic and blocking malicious requests before they reach your website. It uses a set of predefined rules and advanced algorithms to identify potential threats and takes appropriate actions to prevent them. With the Cloudflare Firewall in place, WordPress website owners can significantly reduce the risk of attacks, ensuring a safe and secure online presence.
Choosing the Right Cloudflare Plan for Your Website
When it comes to choosing the right Cloudflare plan for your website, there are a few factors you should consider. Firstly, you need to assess the size of your website and the amount of traffic it receives. If you have a small to medium-sized website with relatively low traffic, you might find that the free Cloudflare plan is sufficient for your needs. This plan offers basic DDoS protection and CDN services, which can help improve the speed and performance of your website.
However, if you have a larger website with higher traffic volumes or if you require advanced security features, you may want to consider upgrading to one of Cloudflare’s paid plans. The Pro and Business plans, for example, offer additional security features such as advanced DDoS protection, web application firewall, and bot management. These plans also come with more advanced analytics and support options. Ultimately, the right Cloudflare plan for your website will depend on your specific needs and budget, so it’s important to carefully evaluate your requirements before making the decision.
Creating a Cloudflare Account and Setting Up Your Website
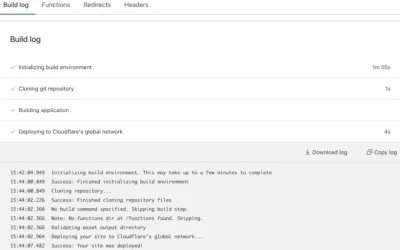
To create a Cloudflare account and set up your website, you need to follow a few simple steps. First, head to the Cloudflare website and click on the “Sign Up” button. You will be prompted to enter your email address and create a password. Once you’ve done that, click on the “Create Account” button and Cloudflare will send you a confirmation email.
Next, you’ll need to add your website to Cloudflare. To do this, click on the “Add a Site” button and enter your website’s URL. Cloudflare will automatically scan your DNS records and import them. You can then review the imported records and make any necessary changes.
After adding your website, Cloudflare will provide you with new nameservers. You’ll need to update your domain’s nameservers with the ones provided by Cloudflare. This step is crucial as it ensures that all incoming traffic to your website is routed through Cloudflare’s network, enabling their security features to protect your site.
That’s it! You’ve successfully created a Cloudflare account and set up your website. Now, all incoming traffic will go through Cloudflare’s network, benefiting from their security features and performance enhancements. Make sure to regularly monitor your Cloudflare dashboard to stay informed about any security events and performance metrics related to your website.
Configuring Cloudflare Firewall Rules for WordPress Security
To ensure the security of your WordPress website, it is crucial to configure the Cloudflare Firewall rules effectively. The Firewall rules act as a protection layer, allowing you to control and filter incoming traffic to your website. By setting up specific rules, you can block malicious requests and safeguard your site from potential threats.
When configuring Cloudflare Firewall rules for WordPress security, there are a few key steps to follow. Firstly, you need to determine the security level you want to apply to your website. Cloudflare offers a variety of security settings, ranging from High to Essentially Off. For most WordPress sites, it is recommended to set the security level to High or Medium to ensure adequate protection. Once you have selected the appropriate security level, you can create specific rules to block certain types of traffic. These rules can target various criteria, such as IP addresses, countries, user agents, or specific patterns in the URL. By carefully defining and configuring these rules, you can significantly enhance the security of your WordPress site.
Understanding the Different Firewall Rule Actions
Firewall rule actions serve as the primary components that dictate how Cloudflare handles incoming traffic to your website. There are various actions available within Cloudflare’s firewall settings, each serving a distinct purpose in enhancing your website’s security. These actions include allowing, blocking, challenging, and simulating actions.
The “Allow” action permits traffic to freely access your website, ensuring that legitimate users can visit and interact with it without any obstacles. This action is useful when you want to whitelist specific IP addresses or enable access to certain resources. Conversely, the “Block” action prevents specified IP addresses or ranges from accessing your website, thus safeguarding it from potential threats or malicious activity. This action is effective in blocking known bad actors or unwanted visitors.
Setting Up Firewall Rules to Block Malicious Traffic
Firewall rules play a crucial role in protecting websites from malicious traffic. By implementing these rules, website owners can effectively block unwanted visitors and mitigate potential security risks. To set up firewall rules to block malicious traffic, it is important to consider the specific threats that your website may be vulnerable to.
One common approach is to block traffic from specific IP addresses or IP ranges that are known for launching cyber attacks. This can be accomplished by creating a firewall rule that identifies the IP addresses or ranges to be blocked. Additionally, it is possible to create rules to block traffic based on certain criteria, such as specific user agents or request patterns, which are indicative of malicious activity. By carefully configuring firewall rules, website owners can bolster their security measures and safeguard their websites from malicious traffic.
Using Firewall Rules to Prevent Brute Force Attacks
Brute force attacks pose a significant threat to the security of WordPress websites. These attacks involve an automated process that systematically tries different username and password combinations until it gains access to the site. To prevent such attacks, Cloudflare Firewall offers a powerful solution by allowing you to set up firewall rules that specifically target and block suspicious login attempts.
One effective way to prevent brute force attacks is by setting up firewall rules that limit the number of login attempts from a single IP address within a certain time frame. This means that if an IP address makes an excessive number of failed login attempts, it will be temporarily blocked from accessing your website. By implementing such rules, you can significantly mitigate the risk of brute force attacks and protect your WordPress site from unauthorized access.
Configuring Firewall Rules to Protect Against DDoS Attacks
When it comes to protecting your WordPress website against DDoS attacks, configuring the right firewall rules is essential. Cloudflare Firewall offers several options to help protect your site from these malicious attacks. The first step in setting up your firewall rules is to identify the typical traffic pattern for your website. Analyzing your website’s usual traffic helps you distinguish between normal traffic and potential DDoS attack traffic.
Once you have a clear understanding of your site’s regular traffic, you can start configuring firewall rules to protect against DDoS attacks. Cloudflare Firewall allows you to create rules based on various criteria, such as IP addresses, countries, or even specific URL patterns. By setting up rules that block traffic from known malicious IP addresses or countries notorious for launching DDoS attacks, you can ensure that your website is shielded from potential harm. Additionally, Cloudflare Firewall provides options to rate limit or challenge suspicious traffic, adding an extra layer of protection to your WordPress site.
Implementing Firewall Rules to Mitigate SQL Injection Attacks
SQL injection attacks are one of the most common and dangerous types of attacks that WordPress websites face. These attacks occur when an attacker inserts malicious SQL code into input fields, affecting the database queries and potentially gaining unauthorized access to sensitive information. To mitigate the risks associated with SQL injection attacks, it is crucial to implement firewall rules in Cloudflare.
Cloudflare Firewall offers a powerful set of features to protect your WordPress website against SQL injection attacks. By configuring specific firewall rules, you can block malicious SQL queries from reaching your server and potentially compromising your website. These firewall rules can detect patterns commonly used in SQL injection attacks and take immediate action to prevent the exploitation of vulnerabilities. With Cloudflare Firewall, you can significantly enhance the security of your WordPress website and safeguard your valuable data from unauthorized access.
Monitoring and Analyzing Firewall Logs for Enhanced Security
When it comes to enhanced security for your website, monitoring and analyzing firewall logs plays a crucial role. Firewall logs provide valuable insights into the traffic that is being allowed or blocked by the firewall, allowing you to identify and respond to any potential threats effectively. By regularly reviewing these logs, you can stay proactive in detecting and addressing any suspicious activity or attempted breaches, ensuring the overall protection of your website.
Analyzing firewall logs helps you understand the various types of threats that your website may be facing. This information allows you to refine your security measures, fine-tune firewall rules, and adapt your strategy to minimize the risk of attacks. By studying patterns in the logs, such as frequent attempts to access vulnerable areas or recurring IP addresses involved in malicious activities, you can make informed decisions on how to strengthen your website’s security and fortify its defenses against potential threats. Regular monitoring and analysis of firewall logs are essential steps in ensuring the ongoing security and integrity of your website.
What is Cloudflare Firewall?
Cloudflare Firewall is a security feature that helps protect your website from malicious traffic and attacks by filtering and blocking unwanted visitors.
Why is WordPress security important?
WordPress websites are often targeted by hackers due to their popularity. Ensuring WordPress security is crucial to prevent unauthorized access, data breaches, and other potential threats.
What are some common threats to WordPress websites?
Common threats to WordPress websites include malware infections, brute force attacks, SQL injection, cross-site scripting (XSS) attacks, and distributed denial-of-service (DDoS) attacks.
How does Cloudflare Firewall enhance WordPress security?
Cloudflare Firewall provides an additional layer of protection to WordPress websites by filtering and blocking malicious traffic, preventing unauthorized access, and mitigating various types of attacks.
How do I choose the right Cloudflare plan for my website?
When selecting a Cloudflare plan, consider factors such as the size and traffic volume of your website, the desired security features, and any specific requirements you may have.
How do I create a Cloudflare account and set up my website?
To create a Cloudflare account, simply sign up on their website and follow the step-by-step instructions to add your website and configure the necessary settings.
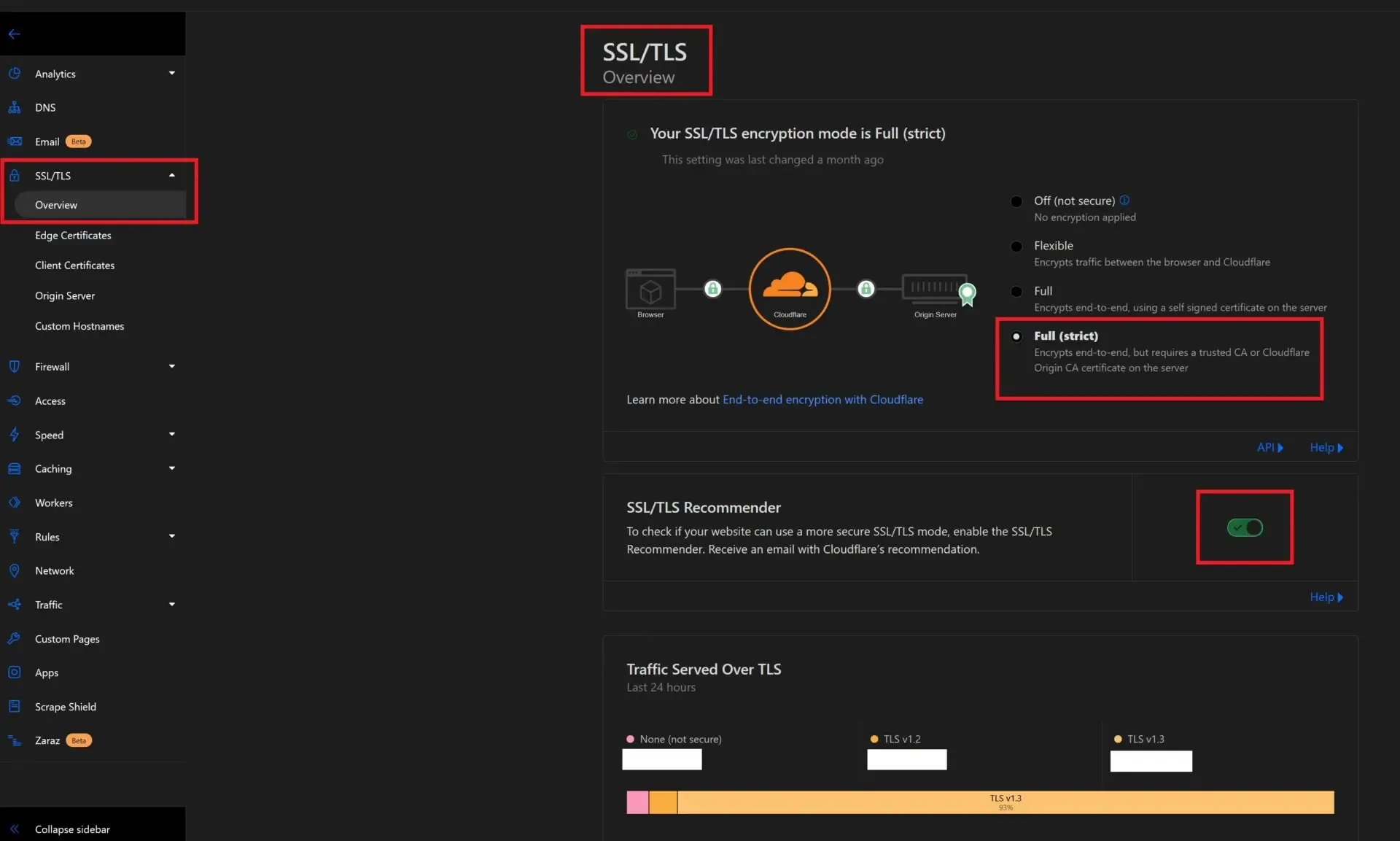
How do I configure Cloudflare Firewall rules for WordPress security?
After setting up your website on Cloudflare, you can configure Firewall rules through the Cloudflare dashboard by specifying criteria and actions to be taken for specific types of traffic or requests.
What are the different Firewall rule actions?
Cloudflare Firewall rule actions include allow, block, challenge, simulate, and log. These actions determine how Cloudflare handles traffic that matches the specified rule criteria.
How can I use Firewall rules to block malicious traffic?
By creating Firewall rules that match patterns or characteristics of known malicious traffic, you can instruct Cloudflare to block those requests or visitors from accessing your website.
Can Firewall rules help prevent brute force attacks?
Yes, Firewall rules can be set up to detect and block repeated login attempts or suspicious activity indicative of brute force attacks, adding an extra layer of protection to your WordPress website.
How can Firewall rules protect against DDoS attacks?
Cloudflare Firewall rules can be configured to detect and block traffic patterns associated with DDoS attacks, effectively mitigating the impact of such attacks on your WordPress website.
How do Firewall rules help mitigate SQL injection attacks?
By creating Firewall rules that inspect and analyze incoming requests for SQL injection patterns, Cloudflare can block or challenge requests that potentially contain malicious SQL code.
How can monitoring and analyzing Firewall logs enhance security?
Monitoring and analyzing Firewall logs allows you to gain insights into the types and sources of security threats targeting your website, enabling you to take proactive measures to enhance security.